Advanced AI, scalable architecture and close service to shield critical information and reduce vulnerabilities.

Benefits
With Gatefy, your company gains much more than email security. Our technology helps reduce risks, increase productivity and ensure compliance with regulations such as LGPD and GDPR.
Complete protection against phishing, ransomware, BEC and spam
Increased productivity, with less time spent on unwanted emails.
Regulatory compliance for critical sectors such as finance, health and government.
Consulting support with experts close to your team.
Benefits
From blocking threats to encrypting messages, Gatefy guarantees complete protection for your company.

Cloud solution, with no need for local infrastructure.
Protects against phishing, ransomware, BEC and zero-day with AI, machine learning and real-time reports. Ideal for companies looking for agility, scalability and reduced costs.
Deployed in your infrastructure, whether physical or virtual, Gatefy guarantees total data control, advanced filters and LGPD/GDPR compliance. In addition to the features of the cloud version, such as high availability and protection against malicious emails, On-Premises offers a customizable sandbox, CDR, URL rewriting and encryption, taking security and customization to the highest level.

Smart choice
Our technology is proprietary and innovative, impossible for scammers to test beforehand, guaranteeing high-level security with a simple and transparent experience.
Smart choice
Our platform covers all stages of email communication: from incoming messages to preventing internal leaks.

Protection against spam, phishing, ransomware and BEC.

Prevents leakage of sensitive information and intellectual property.

Compatible with Microsoft 365, Google Workspace, Exchange and Zimbra.
DMARC, SPF, DKIM, email encryption and archiving.
How it works
Our platform uses artificial intelligence, machine learning and advanced natural language processing (NLP) to analyze each email in real time, identify suspicious patterns and prevent attacks from reaching your team.
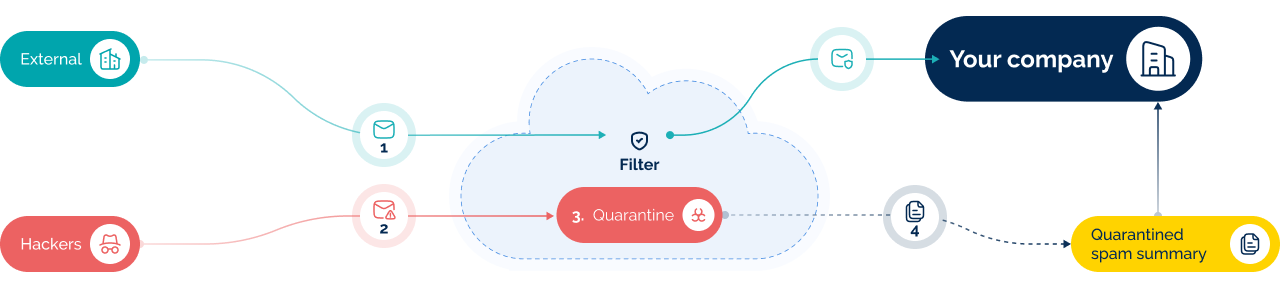
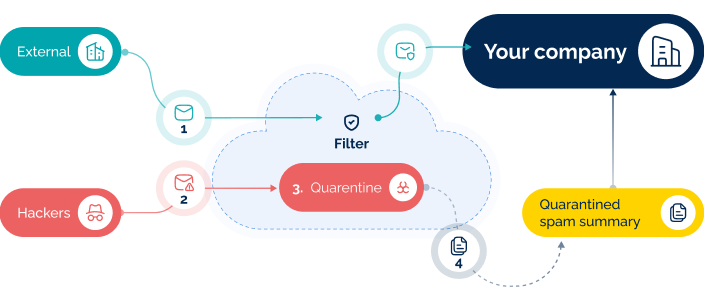

1
All external emails go through Gatefy's filter, where they are analyzed in real time to identify suspicious content or phishing attempts.
2
The filter applies layers of security (AI, reputation, authentication and content analysis) to detect spam, phishing, malware and other risks. If there is a threat, the flow is stopped before it reaches the company.
3
Dangerous messages are isolated in quarantine, where they are available for review, preventing fraudulent content from reaching employees.
4
In addition to the quarantine, the company and its users receive a daily summary of blocked emails. Access can also be made via the browser, from inside or outside the company.
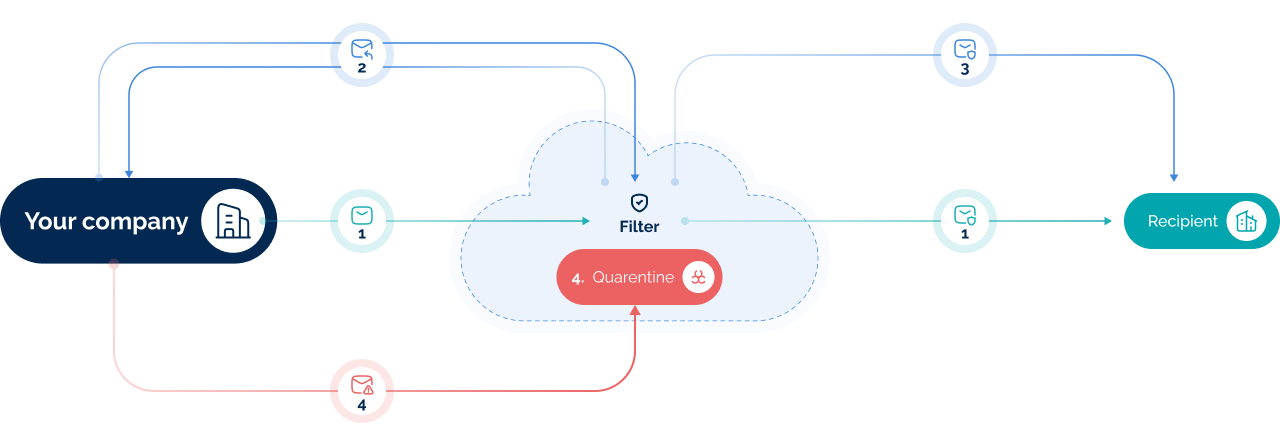
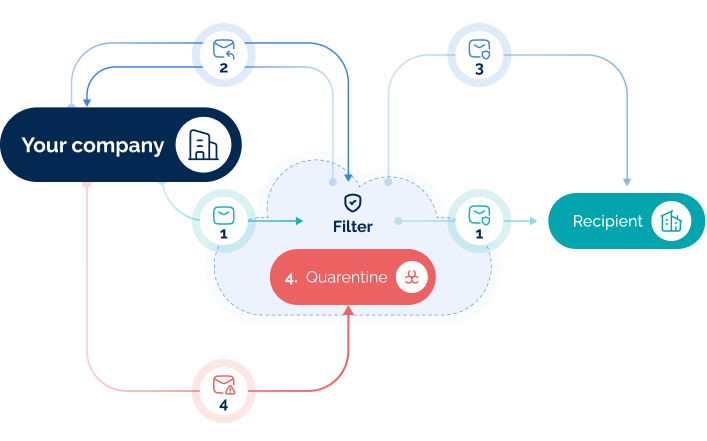
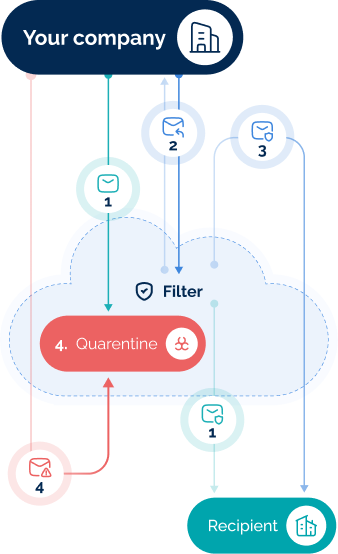
Valid and compliant emails pass through the filter without restriction and are sent normally to the external recipient, ensuring reliable deliverability.
When an email contains information protected by compliance policies, it is withheld and returned to the company with a notice for manual review and release.
When there is compliance, the email is delivered to a trusted recipient.
When it identifies a threat, the filter blocks the e-mail and sends it to quarantine, notifying the company without allowing the message to return to the internal environment.
Success stories
From financial institutions to healthcare groups, Gatefy helps organizations reduce phishing incidents, prevent data leaks and maintain business continuity.
Less phishing, more security in everyday life
Joaquim Ebeling
Infrastructure Supervisor
We gained productivity and peace of mind
José Carlos Pereira Junior
IT Infrastructure Supervisor
Deliverability restored on the very first day
Eliana F. Cascaes Correia
IT Manager
Complete protection against modern threats
Laércio Santo de Araujo
IT Manager
Peace of mind to focus on what matters
Fabio Junior
IT Manager
Resources and content
Here you will find exclusive content to support your team in making strategic decisions: articles on the latest threats, good protection practices, success stories and technical materials such as whitepapers and datasheets.
Browse by category
10 real and famous cases of BEC (Business Email Compromise)
10 real and famous cases of BEC (Business Email Compromise) BEC (Business Email Compromise) scams have been a major concern for businesses and governments. In this type of attack, cybercriminals
8 reasons to use DMARC in your business
8 reasons to use DMARC in your business A major cybersecurity problem is: hackers are always looking for new approaches and ways to abuse company brands and domains to trick

What is mail server?
What is mail server? We can say that an email server (or mail server) is your digital postal service. It’s a machine or application responsible for handling messages. In other

What are RUA and RUF in DMARC?
What are RUA and RUF in DMARC? DMARC (Domain-based Message Authentication Reporting & Conformance) is an email validation and authentication system used to detect fraud, such as phishing and impersonation,

10 real and famous cases of social engineering attacks
10 real and famous cases of social engineering attacks Social engineering is the tactic behind some of the most famous hacker attacks. It’s a method based on research and persuasion

Sextortion scam demands USD 2000 to not “ruin your life”
Sextortion scam demands USD 2000 to not “ruin your life” Sextortion campaigns continue to flood email boxes of several people. These scams generally have the same modus operandi. To understand
Protection in practice
Talk to our experts and find out how Gatefy can protect your data, your team and your brand’s reputation with simple, scalable and efficient solutions.
