Scammers hijacked GoDaddy domains to apply bomb threat spam and other attacks
- Updated at March 18, 2021
- By Gatefy
- Blog, Security News
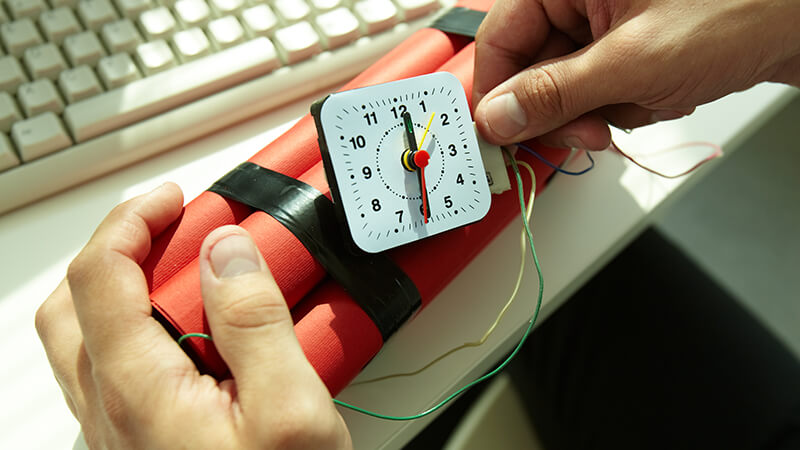

The spam campaign that demanded payments of USD 20,000 in bitcoin under the threat of blowing up businesses, schools and other places in several countries, including the US and Canada, in the past month, has probably exploited a GoDaddy flaw.
As Ars Technica reported, with the support of anti-spam researcher Ronald Guilmette, the flaw allowed spammers to hijack thousands of domains belonging to well-known and legitimate companies, such as Yelp, Expedia and Mozilla. The flaw left more than 500,000 domains vulnerable to hijacking.
It’s also known that the bomb spammers used the exploit for other types of spam attacks as well, including a sextortion campaign and frauds involving parking tickets and package delivery. Since the domains hijacked had a good reputation, the scam gained legitimacy, leaving many people on alert.
According to Guilmette, many of the hijacked domains have used IP addresses from Reg.ru, a russian hosting provider, and they had been transferred from GoDaddy before the attacks began. He named the spammer group as Spammy Bear.
To summarize the flaw, attackers took advantage of the fact that many domain owners don’t keep their name server information updated when removing a zone file. Besides that, many hosting companies that offer managed DNS services don’t make a full verification when people add domains to their accounts.
Cybersecurity researcher Matthew Bryant has already talked about this subject, detailing the problem, in one of his post, Floating Domains, in 2016.
To have your domain and website protected in a situation like this, you need to ensure that your data, your name server information, is always up to date.




